Why everyone should use a password manager
Apr 22, 2020
Video script writing
May 6, 2020As regular readers will know, I am on something of a minor crusade to help people learn more about data security and online privacy. Alongside my main work at Coastal Content, I ghost write a ton of articles and tutorials on the subjects of cyber security, online privacy, data security, encryption and all that good stuff. Today I am going to talk about hash and salt and how they help protect your online accounts.
Most websites that you interact with require some form of login. As part of that login, you will have to provide a username and password. If you’re lucky, the website will also provide two-factor authentication. If you’re not, it won’t. Either way, your password is the primary protection on that account.
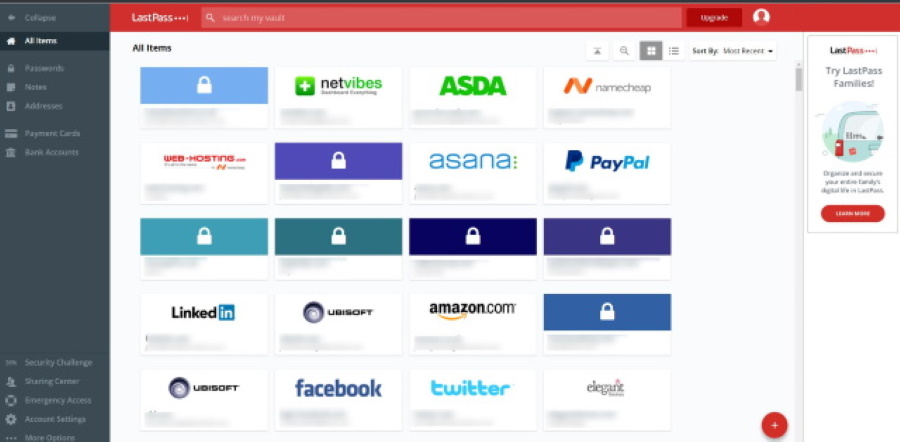
As we know, passwords are not the most secure. We have to balance strong passwords with being memorable. Remember dozens of them at a time and be able to quickly recollect them whenever we need to log in. Or we use a password manager. Either way, we know passwords are not the most secure security methods in the world.
Passwords can be stored in two main ways, plain text and hashed. Plain text passwords are exactly as the name implies. A password of ‘abc123’ is stored on the database as ‘abc123’. As you can imagine, that isn’t very secure. Which is where hash and salt come in.
Facebook has been accused of storing employee passwords in plain text. Google has apparently stored G Suite user passwords in plain text. A database of 773 million plain text passwords was for sale on the web last year. All from organisations that really should know better. They aren’t and won’t be, the only ones who store passwords in plain text either.
What they should be doing is salting and hashing.
Salting essentially means adding random characters to a password to disguise it. Hashing means encrypting and scrambling that salted password to make it even tougher to crack.

Salting
Want some salt with that? Salting is used alongside hashing to add some randomness to a password. If a website has fifteen users who all login with the password ‘abc123’ all fifteen password hashes will look the same, which is an obvious weakness.
That’s where salting comes in.
Salting adds a random set of characters to every password before it is hashed. Like the hash values, an algorithm controls the number and type of characters. Typically, salt is added before the actual password and will be truly random.
For example, the password of ‘abc123’ would be salted so it looks something like ‘c0e81794384491161f1777c232bc6bd9ec38f616560b120fda8e90f383853542abc123’. Typically, if the website uses 256-bit encryption, it will use 256-bit salting.
Peppering
Peppering is also a thing. It is similar to salting but is added at the end of the password. This isn’t so widely used but is another way to strengthen passwords.
Hashing
Hashing is the process of scrambling a password you enter into a website. Rather than storing it as plain text in a database, a responsible website will perform a hash. This scrambles your password so it is unintelligible. That hash is then given a unique value which is shared between the login server and the authentication server.
In an ideal setup, when you log into the website, the password server recognizes the password you enter and compares it to that unique hash value. It sends the hash value to the authentication server for verification. If the value matches, you can log in. If it doesn’t, you are asked to try again.
The actual password is never shared between the two servers only the hash value.
Hashing depends on an algorithm that is shared between the password and authentication servers. As long as the two servers know the algorithm, your login should work perfectly.
For example, a password of ‘abc123’ could be hashed as ‘2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824’.
A password of ‘aac123 could be hashed as ‘58756879c05c68dfac9866712fad6a93f8146f337a69afe7dd238f3364946366’.
As long as both servers or services know what algorithm to use, logins should always work.
Protecting your passwords
When you sign up to a quality website, your password will first be salted and then hashed with SHA-2 or newer algorithms. If the site uses peppering, that will be added after the salt before being hashed. So rather than storing your ‘abc123’ password, the password server will have something that looks like ‘2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824 c0e81794384491161f1777c232bc6bd9ec38f616560b120fda8e90f383853542abc12’.
The exact length of the password will depend on the strength of the salting but you get the idea.
It is that code of nonsense that is stored in the password database and that is transferred between a login server and authentication server. As long as both servers know the salt and hash algorithms, it can decipher the login and either allow or deny access.
Should the website be hacked or come under attack, many of the more popular hacking methods such as brute force or dictionary attacks won’t work. The hashed password isn’t in a dictionary and makes no sense except to the algorithm used to generate it. The time it would take to crack the password would be prohibitive and any website owner who is half awake would notice it.
Hashing and salting are not perfect but they are pretty effective. As long as the website uses a newer algorithm such as SHA-2, Bcrypt, PBKDF2 or Scrypt, your password should be relatively safe.
The guys over at Private Internet Access cover hacking and security in a lot more detail. Check out their hacking basics post.




